Checker of Anonymity and IP address
There are many sites where you can check your IP address and other network settings. Such checks help to understand what can give out the real location.
For many years we used the checks on the Whoer and 2IP websites and recommended them to our customers.
Why did we make our anonymity check and IP address?
Our VPN and proxy service is associated with anonymity, so we often visited these sites ourselves and checked the IP address. As a result of an infinite number of tests, we began to notice bugs and inaccuracies in the work of these sites.
We wrote that they removed the bug with the incorrect DNS server definition.
The site determines the main IP address of the server and indicates it in the list of DNS servers. If you run a DNS query using the main IP address of the server with the command nslookup google.com [IP Server], this request will not be executed. This indicates that this IP address is not a DNS server and it does not need to be added to the list of DNS servers on the site.
Another bug is related to the definition of anonymity through the module p0f and the interpretation of data.
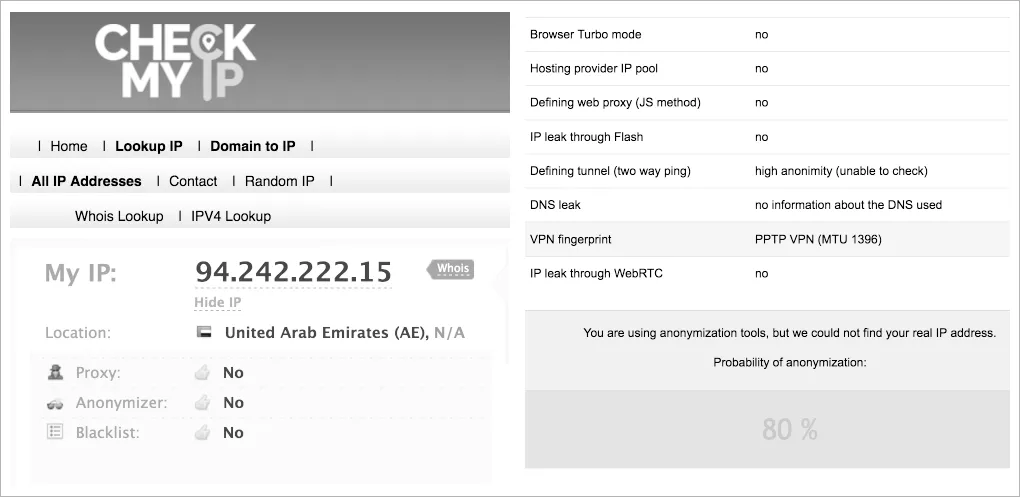
The p0f module can determine the MTU values and compare it with the MTU reference values for the VPN with different types of encryption. If the MTU value corresponds to some type of VPN from the reference table, then p0f indicates the use of the VPN. If a specific MTU value is not in the database and it is less than 1400, then p0f always indicates that a VPN is defined.
The developers of p0f did not take into account that the system administrator can manually change the MTU value for connections and then ALL connections will be considered VPN connections. Some mobile ISP use MTU <1400. As a result, this error was not corrected at the IP address verification site and it is always shown that a VPN.
Interpretation of data on the use of Anonymizer.
Another bug in the definition of Anonymizer. A large amount of IP addresses that are not used for VPNs, proxies, etc., is defined as the use of Cyberghost VPN and then the status changes to Anonymizer: Yes.
We wrote about this bug in support. The answer was simple: there may be errors in our database.
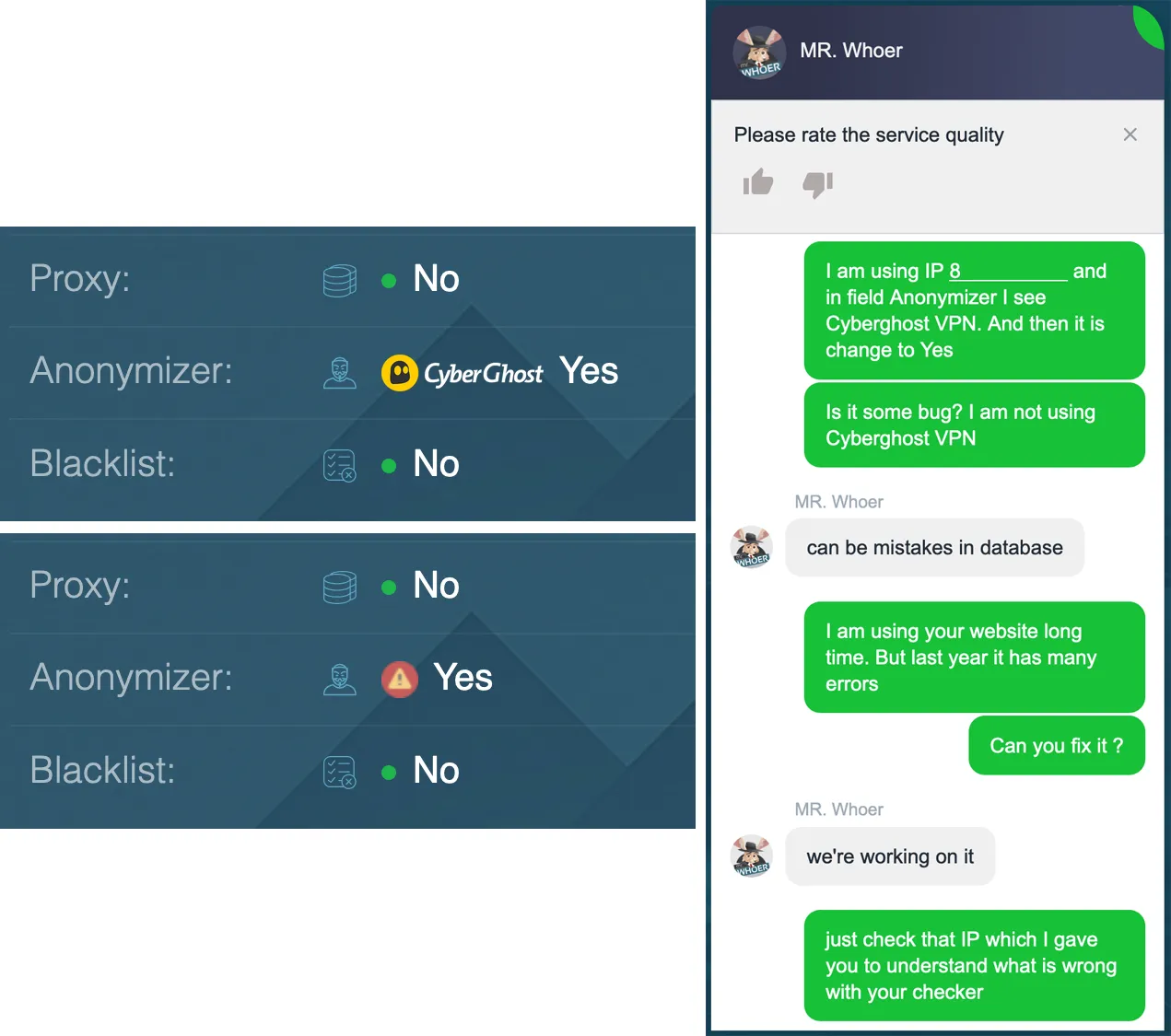
We were not heard and the checks on those sites also work with errors.
Anonymity check based on facts, but not conjecture
It was important for us to provide a quality product that would take into account requests from customers. It is important for us to show truthful checks and point out what really matters. Many anonymity checks are now empty and have the form of guesswork, the probabilities that this is so.
We wanted to make an anonymity check so that it was accurate. We have become experts in the verification of anonymity and now we want to tell you which checks are based on facts, and which are on conjectures.
Check your anonymity and IP address
Creativity at the intersection of technologies
We revised the anonymity checks on more than 10 sites and selected all the most important. Then we combined the checks from all popular IP address verification sites into a convenient table. Now you can find out all about your anonymity on one page.
So, let's analyze all the checks in detail.
Color banner
By banner, you can immediately understand - Everything is fine or There are things to think about.
The banner has 3 colors: red, yellow and green. Only a green banner guarantees perfect anonymity.

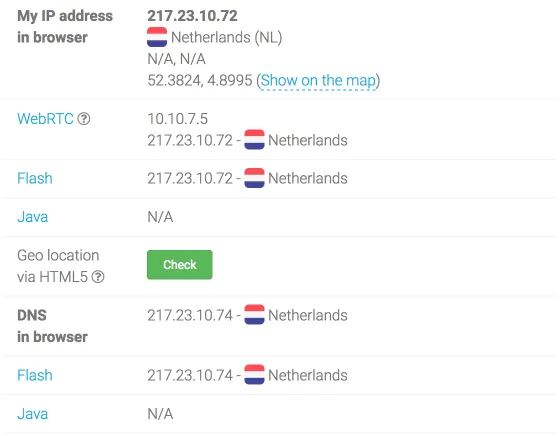
Check IP address and DNS servers
The main unit checks IP addresses and DNS servers in various ways. The checks are implemented through PHP, JavaScript, WebRTC technology, Flash and Java. If the countries are different, they will be underlined in red.
The verification of Geolocation via HTML 5 is made in a separate button, since it presents a high risk of real location detection if you use the Wi-FI module on your device.
The function of Geolocation via HTML 5 takes the coordinates of the GPS device from the Wi-Fi module bypassing the VPN, proxy, TOR and all other ways to remain anonymous. We recommend using a wired Ethernet connection and disconnecting the Wi-Fi module.
Super Anonymity check
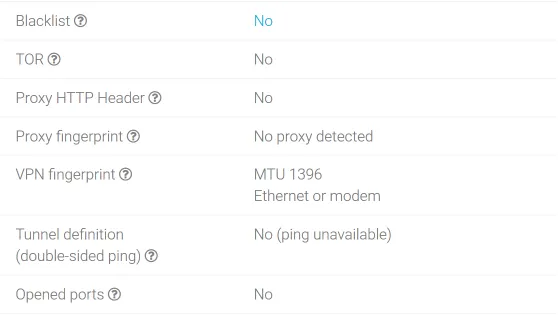
Blacklist
The IP address is checked for presence in Blacklist. If the IP address is present in the Blacklist, then some services can block this IP address (for example, block the delivery of mail from this IP address). The presence of an IP address in Blacklist does not affect your anonymity in any way.
Tor
On the Internet there is a list of open nodes of the Tor network. If the IP address is on this list, then you are using the TOR network. You are anonymous, but it means that you have something to hide and some websites can block content for such users.
Proxy HTTP Header
Proxy HTTP Header checks for proxy fingerprints in browser headers. Use anonymous proxy or socks 5 protocol to avoid detection.
Proxy fingerprint
Proxy fingerprint based on module p0f checks the browser's fingerprints on the use of the proxy.
VPN fingerprint
The main purpose of a VPN fingerprint is to identify the use of a VPN. The p0f module recognizes the value of the MTU connection and, based on this, makes a conclusion about using the VPN.
As we wrote at the beginning of the article, we eliminated the incorrect output of data in the p0f module and left only the values that 100% claim to use the VPN. As a result, we received a true assessment of your anonymity.
It should also be noted that the p0f module does not have time to develop behind VPN technologies and contains outdated stamps identifying VPN connections.
Double-sided ping
A two-way ping between the client and the server helps determine if there is a tunnel (usually a VPN tunnel or a proxy). If the ping values are very different, this indicates the use of the tunnel.
Open ports
Open ports are checked on the specified IP address. If the standard IP and proxy ports are opened on the IP address, then it is likely that you are hiding your real location. ISP always block specified ports.
For example, the standard port OpenVPN 1194, Socks proxy 1080, IPSec VPN 4500 and 500, the Web proxy uses 8080 port.
We use an extended list of standard ports and check TCP and UDP connections. If we find an open port from the table, this indicates that the VPN or proxy is used on this IP address. You remain anonymous, but websites may restrict content to such users.
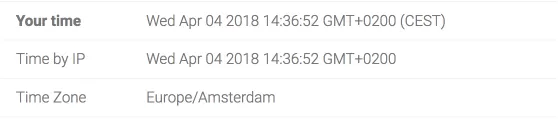
Time zone check
Compare your time zone, installed locally on the device and the time zone that is used for this country by IP address. If they differ, it is highlighted in red.
Operating System Check
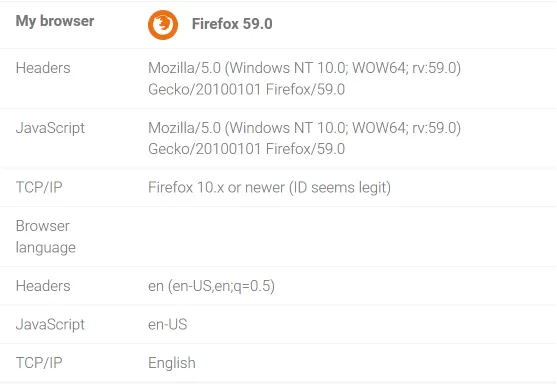
The values obtained from the browser headers, through JavaScript, the p0f module are displayed and the operating system is determined.

Browser check
Browser headers, via JavaScript, the p0f module are checked. Then the browser version and the language used in the browser are determined. Configure the browser so that the languages used in the country are displayed by IP address.
Enabled Technologies
We check if you have enabled technologies that can tell you about your real location.
We recommend that you turn off these technologies for perfect anonymity. Some websites may not work correctly without the specified technologies.
Our website requires JavaScript and Cookies to work properly. We are working hard to rid our site of these requirements.

Checking your anonymity
Our check of Anonymity and IP address completely replaces the use of all other sites. We reviewed over 10 different sites to collect all the important checks on 1 page.
Check your anonymity and IP address
If you have suggestions and wishes, we will be happy to know about them. Write to the section Ask your question.
Become an expert!
Get more information on how to be anonymous on the Internet.
Get knowledge in 1 click