How to set up Tor Browser
If you do not know what is this Tor Browser then read article what is a Tor network.
Download Tor Browser only from the official site torproject.org.
Be careful! There are sites that mimic the Tor Project website. For example, the site torprojectS.org (added the letter S at the end) is trying to install on your computer a trojan. Do not download Tor Browser on third-party sites.
By the way Tor Browser is made based on the Mozilla Firefox browser, since it is the only browser able to work independently with Socks connection without an operating system.
Download Tor Browser from torproject.org
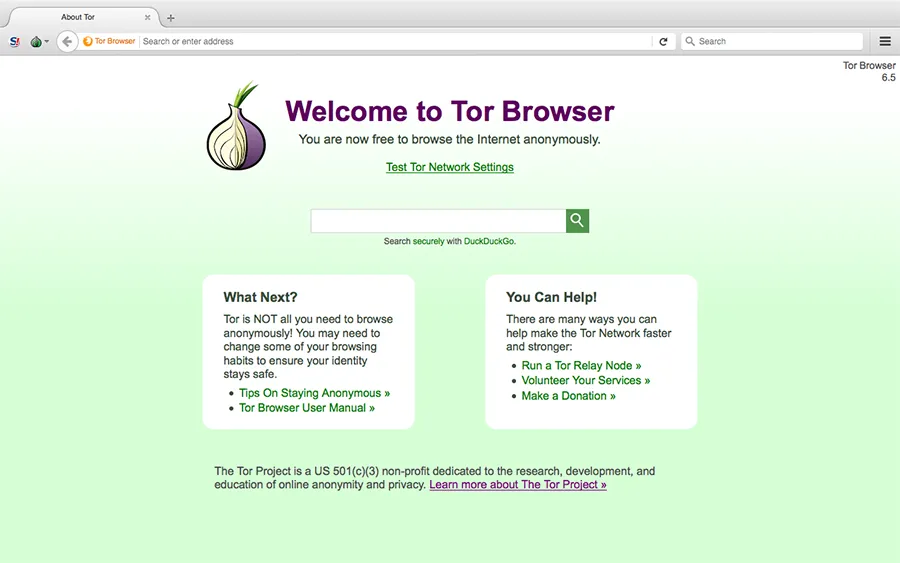
After installing Tor Browser is fully operational. Below is a screenshot from the official website.
Recommended use Tor Browser
- do not install additional plug-ins, as it is likely to install a plugin that will give your actual location. All the necessary plug-ins are already installed for anonymity.
- do not open the documents (eg, PDF and DOC) while you are online. In such files can be embedded macros that have requested access to the Internet directly from the program, bypassing the Tor network. This compromise the your real IP address.
- do not download torrents on the Tor network, as it will increase the load on the network. Torrent program are arranged so that they always get access directly to the Internet, and do not consider the proxy settings. It can compromise your real IP address.
- use the https connection is always. This connection will ensure the security of data transmission.
Tor Browser Main Window.
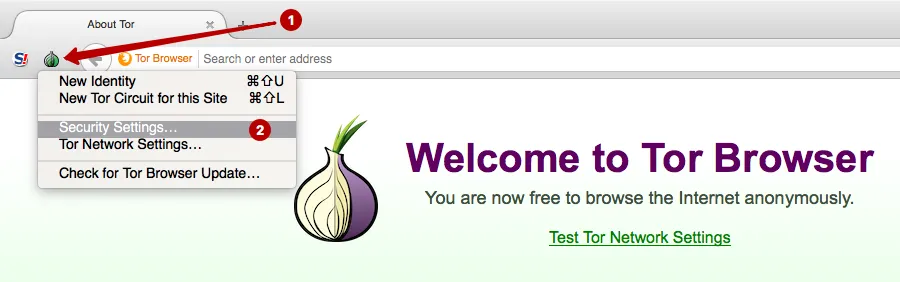
Click Security Settings.
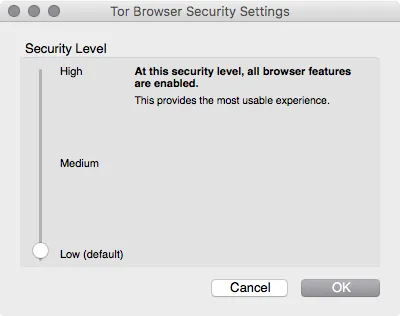
Set the security level:
- Low (default) – Standard security.
- Medium – Javascript is disabled on sites that do not support https. HTML5 video and audio is triggered by clicking through the NoScript plug-in
- High – Javascript is disabled on all websites. HTML5 video and audio is triggered by clicking through the NoScript plugin. Not allowed for loading certain types of images, fonts and icons
Suitable for most users. Web sites are opened correctly and nothing is blocked.
Since most Web sites use Javascript is, therefore, to view websites in High mode is problematic, since the content is hidden. We recommend this mode when you want to read an article on some website, it is not necessary in this case to authenticate online.
Tor Browser is ready for use, and you can immediately begin to surf anonymously.
Note that using this setting only Tor Browser uses the Tor network. All other programs are using a direct connection to the Internet and send your real IP address.
What to do with the programs that are not able to work directly with the Socks protocol? For example, e-mail clients, and other browsers, instant messaging programs, etc. We recommend the use of Proxifier to redirect traffic of such programs in the Tor network.
Setting Proxifier through the Tor network
Proxifier program can:
- redirect traffic from all of the operating system software through a proxy (including e-mail clients, browsers, instant messaging programs)
- create proxy chains
- use the DNS server from the proxy, hiding the real DNS of ISP
- supports http and socks proxy
Download Proxifier for Windows Download Proxifier for macOS
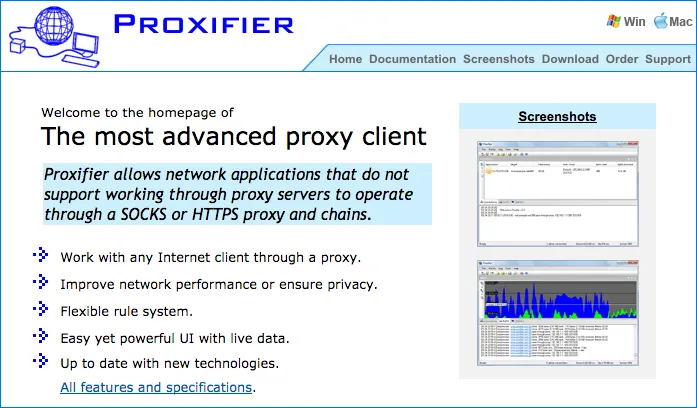
Home page of official site Proxifier.
Install the program Proxifier. This program is able to collect the traffic from operating system and flowing through a certain proxy server.
To configure Proxifier need to learn use the Tor network port. Go to the Preferences in Tor Browser.
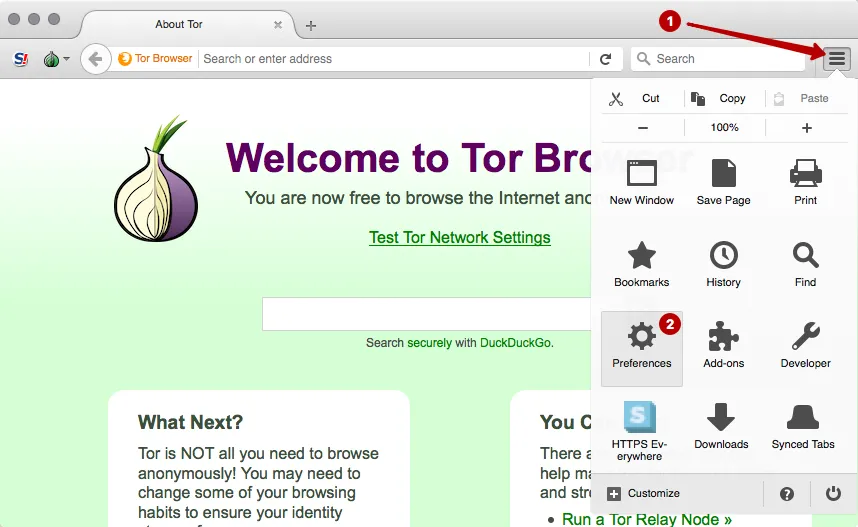
Select the Network Settings.
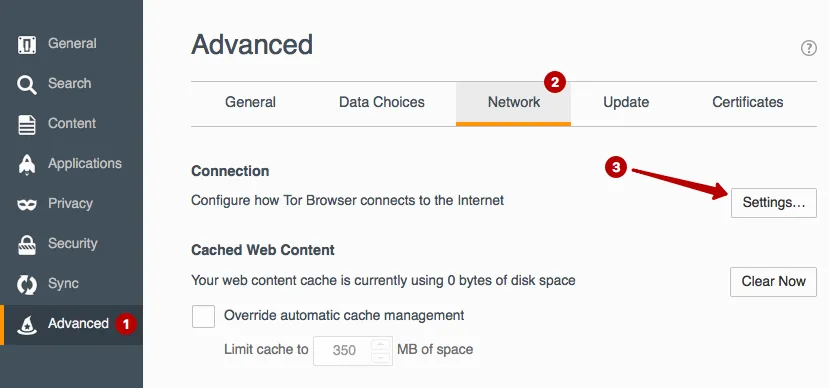
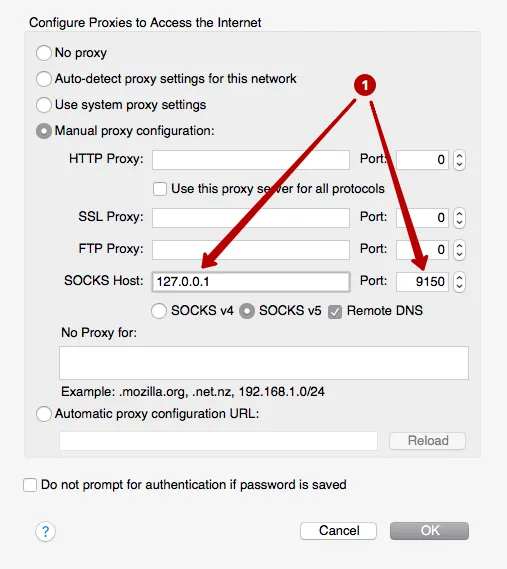
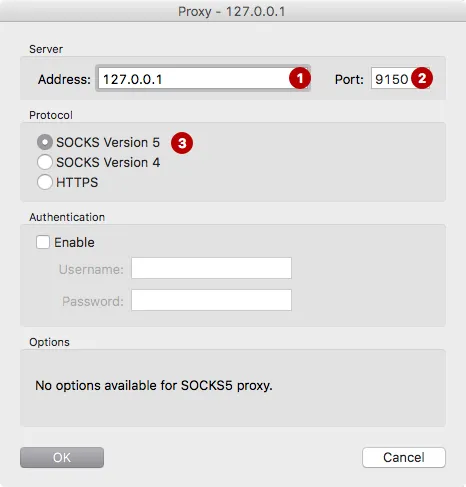
See use the local IP address and port of the Tor network connection. These data must be inserted in the program Proxifier to the entire operating system, traffic was held in the Tor network. In this example, 127.0.0.1 and port 9150.
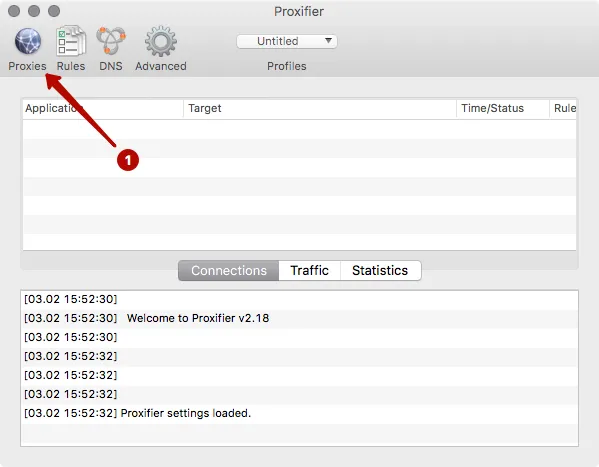
Run app Proxifier.
ATTENTION! It is important first to start Tor Browser and wait until the main window appears. And only after that start the program Proxifier.
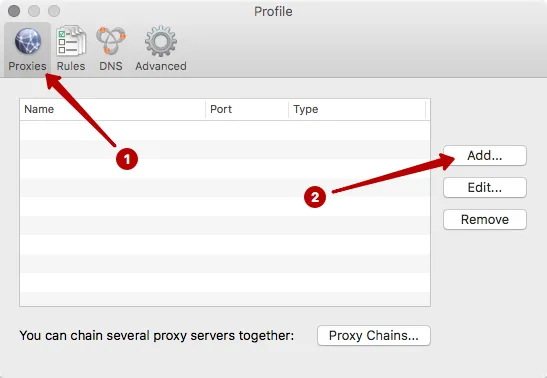
Click on the Proxies button.
Click to Add.
Enter IP address and port. In our example: 127.0.0.1 and port 9150.
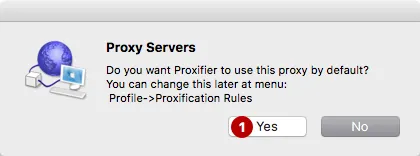
Click Yes - agree to use proxy by default.
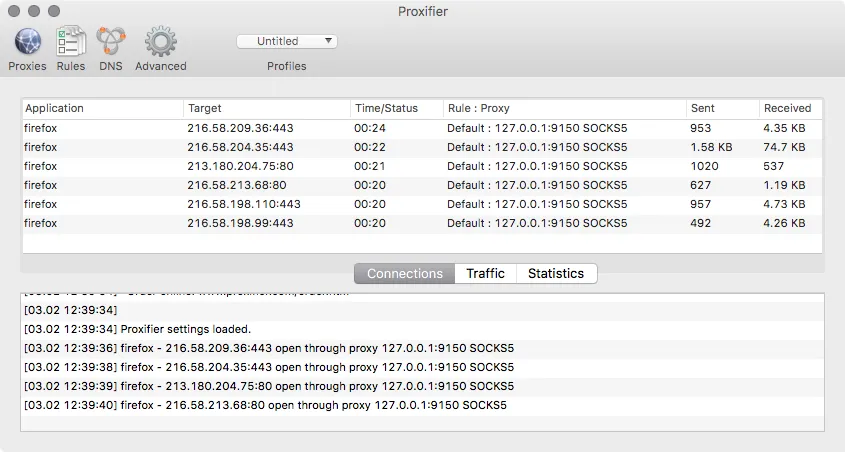
Open any browser or email program. In the program Proxifier you will see a list of connection through the Tor network. In any browser you can check your IP address and to make sure that will show the IP address of the Tor network, and not your real IP address.
If something does not work, close the Tor Browser and Proxifier. And then start the Tor Browser and wait for the main window. Only then run Proxifier. No additional configuration is not necessary to do. All traffic will automatically go through the Tor network. Close the program Proxifier, to reclaim your real IP address.
Do you need VPN?
Try our anonymous VPN without logs
We guarantee to refund within 7 days after purchase
